* As of May 1st, 2025 this site will no longer be updated.
Please visit https://www.ai.mil/About/Organization/DDS/ for the most up-to-date information about the Defense Digital Service function. CDAO continues to integrate and consolidate digital service functions to provide maximum value to the warfighter. We persist in aligning all capabilities against the priorities of the Department and execute our mission of enabling the rapid and scaled adoption of data, analytics, and AI.
Our Work
DDS tackles complex challenges head-on by recruiting exceptional tech talent from the private sector and putting them to work inside the Pentagon.
Projects include reforming digital services that provide military families access to critical benefits, running bug bounty programs to identify vulnerabilities and better secure defense systems, developing drone detection technologies, keeping adversaries off of defense networks, rethinking training for cyber soldiers, and more.

RAPID CAPABILITIES
When a DoD organization faces a technical issue that cannot wait, DDS steps up to the challenge.
These engagements might result in a swift technical fix, implementing new practices, or transitioning a new capability to a partner in the department.
CYBERSECURITY
At DDS, a project isn’t done until it’s secure. DDS is known as the birthplace of Hack the Pentagon, the first bug bounty program in the federal government, as well as countless other programs that keep systems safe and secure.
TECHNICAL ASSESSMENTS
DDS partners with organizations all over the department to help them assess their next steps.
This might be in the form of evaluating existing efforts to figure out what's broken, or we may be helping them identify the core problem they are facing.
Rapid Capabilities
Rapid response projects give DDSers opportunities to jump in and make an impact in unprecedented ways. Whether it's responding quickly to support the evacuation of Afghanistan, working to streamline some of the most onerous hiring practices in the federal government, or helping to keep service members safe from enemy drones, our team has what it takes to get the job done.
Counter - UAS

DDS's technical experts rapidly field low-cost counter unmanned aerial systems (cUAS) solutions to support the warfighter's need for real-time detection, tracking and mitigation of cUAS threats. Since adding cUAS as a portfolio in 2020 through the Rogue Squadron acquisition, DDS programs have built best-in-class capabilities that are used domestically and globally, and continue to strengthen and modernize the DoD's defensive posture.

Desert Architect

In May 2024, DDS, in partnership with the U.S. Army and United States Central Command (USCENTCOM), conducted a week-long hackathon to improve force protection challenges associated with countering one-way unmanned aerial systems (UAS). The team developed proofs of concept and recommendations in data interoperability, system health status, incident reporting procedures, and force protection system usability, many of which are being incorporated into the current systems of record.

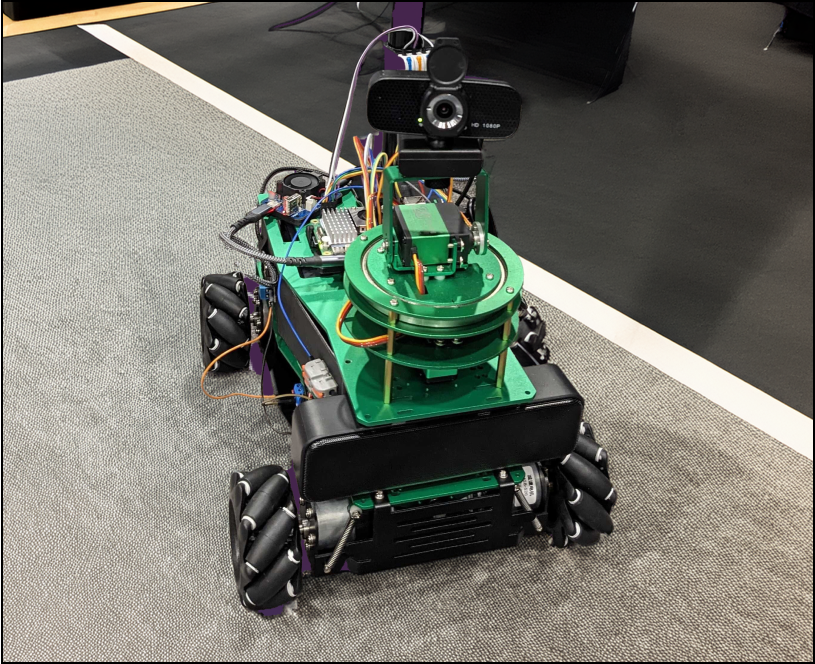
Combee
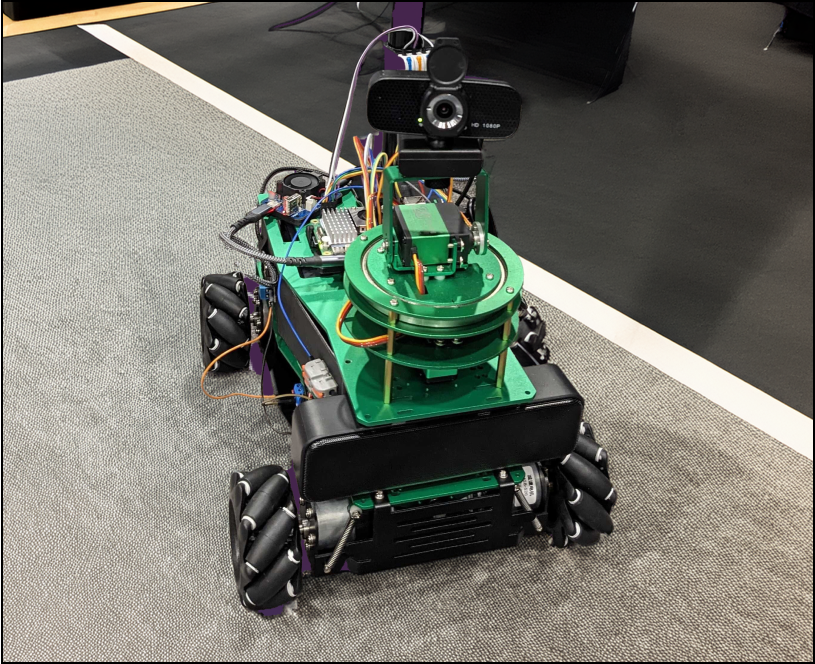
As a part of DDS's experimenting with AI at the tactical edge, DDS developed Combee, a framework for using Large Language Models as an interface for existing physical systems and equipment. Using generative AI models as an alternative front end, Combee allows operators to communicate and operate systems using plain language, reducing the amount of jargon the models need to learn and training they need to go through.
Axon - Large Language Model Operations Framework
DDS developed Axon, DoD’s first large-language model operations (LLMOPs) framework to align large language models to DoD domains. DDS released a fine-tuned LLM, axon-7b-policy, using this framework to enable boosts in chatbot performance against DoD policies and issuances. Axon was the first LLM deployed to a DoD High Performance Computing Center. Axon proves that AI can be used to chat with DoD data to assist with numerous daily tasks, and can evolve to include voice prompts and text to speech capabilities that will adapt and learn from users.
Code.mil

Code.mil is the Department of Defense's public inventory of open-source and custom-developed software, supporting the Federal Source Code Policy by promoting transparency, reuse, and collaboration. It provides a platform for discovering DoD-released source code and helps developers navigate open-source contributions within the DoD. By cataloging publicly available projects, Code.mil facilitates the sharing and reuse of custom-developed code across the federal government and with the public, reducing duplication and driving more efficient software development.

Bastion

Aerial refueling is crucial for various missions, allowing tanker aircraft to fuel receiver aircraft in flight. However, many processes are manual, leading to inefficiencies such as wasted fuel and man hours. DDS is leading a pilot to optimize aerial refueling operations in the Indo-Pacific theater, focusing on integrating advanced digital technologies and constraint optimization algorithms into existing processes. The pilot will streamline tanker-receiver pairing, optimize routing, and enable data-driven decision-making, with the goal of enhancing efficiency, fuel savings, and mission effectiveness.

Move.mil

DDS developed the highly successful website 'Move.mil', which is specifically designed to assist military personnel in managing their household goods during a Permanent Change of Station (PCS). A PCS can be one of the most significant and stressful challenges a soldier faces. Move.mil alleviates the pressure of scheduling, customer service, and locating other important information by consolidating all these resources in one convenient location. Since its launch, Move.mil has been integrated into the Military OneSource platform and is expected to save the military over 3,000 weeks annually in lost productivity during the busy PCS season.

82nd Airborne AmmoOps

In partnership with the 82nd Airborne, DDS developed a minimally viable application called AmmoOp that streamlines and simplifies ammunition ordering for use in training exercises. Initial testing of AmmoOp indicated it will save the 82nd Airborne more than 8,900 soldier-hours annually.

Magic Manifest

Safety and efficiency are vital for jump masters in the 82nd Airborne. DDS partnered with the 82nd Airborne Innovation Unit to develop an application that streamlines the aircraft boarding process and reduces paperwork during airborne training events. The app enables jump masters to scan troops' id cards during pre-checks and boarding, ensuring all personnel are accounted for. The app helps jump masters make last-minute decisions, as well as enhances safety, tracks combat readiness, and reduces administrative burdens while showcasing technology's benefits for military operations.

Cybersecurity
Cybersecurity is a part of everything we do at DDS. From our flagship Hack the Pentagon bug bounty program to implementing a DNS resolution service that combines threat intelligence with public sector best practices, to protecting supervisory control and data acquisition (SCADA) and industrial control systems (ICS), we help maintain the stability of critical systems and traditional networks that countless people rely on every day.
Hack the Pentagon

Hack the Pentagon (“HtP”) leverages the power of the crowd on priority critical cybersecurity initiatives to substantially improve the DoD's cyber defenses through a series of “bug bounties”. In a bug bounty, DDS works with asset owners, industry partners and independent security researchers to discover and document vulnerabilities. With this approach, DDS helps the Department quickly mitigate vulnerabilities to strengthen the DoD's cybersecurity posture.

DEF CON

DDS has participated in DEFCON since 2019, hosting educational workshops and contests on everything from hacking power grids to satellites, and everything in between. We've been honored to partner with multiple Villages to inspire and educate the next generation of hackers and security researchers to help solve the problems that affect us today. If you want to see all of our workshops, past and present, check out our github

Technical Assessments
Technical Assessments are one of the corners of our work where our human-centered approach and hands-on technical knowledge combine to elevate the technology and services within the DoD. By going where the work is, we are able to do hands-on research with the target user group to really understand their real-world constraints.
We endeavor to help our partners solve the right problems by asking the right questions. Because these projects are mostly internal with our partners, we don't share the details publicly.