* As of May 1st, 2025 this site will no longer be updated.
Please visit https://www.ai.mil/About/Organization/DDS/ for the most up-to-date information about the Defense Digital Service function. CDAO continues to integrate and consolidate digital service functions to provide maximum value to the warfighter. We persist in aligning all capabilities against the priorities of the Department and execute our mission of enabling the rapid and scaled adoption of data, analytics, and AI.
We deliver better services to the warfighter through design & technology.
Defense Digital Service (DDS) is part of the Department of Defense’s Chief Digital and Artificial Intelligence Office (CDAO), working to tackle the department’s highest-priority digital challenges.
Our Vision
A Defense Department where people are enabled by technology, not limited by it. To accomplish this, we hire technical talent from industry on limited two-year terms who are focused on delivering high-impact solutions and advanced capabilities to protect national defense.
U.S. Senate Committee on Armed Services, Subcommittee on Personnel — on DDS
“…I found that getting to the truth...and getting to the bottom of something, that they operate at a much greater speed…”
"Progress is not inevitable, progress is intentional."
- Glenn Parham, DDS Alumnus
Our Values
Show, Don't Tell
We rapidly demonstrate and deliver capabilities.
Go Where the Work Is
We show up and experience the problem first hand to understand the users' challenges.
Make a Difference
We leverage our technical expertise to improve the lives of service members and civilians.
Be Brave and Speak The Truth
We tell the truth about systems, capabilities, and processes — even if it's hard to hear.
Design With Users
We rapidly demonstrate and deliver capabilities.
Our Story
Founded in November 2015, DDS brings best practices and technologies from the private sector and pairs them with the critical mission of the Department of Defense. DDS brings in America’s best and most innovative talent in their fields to transform the DoD.
Testimonials From Our Partners
DDS has been an invaluable partner in providing counter unmanned aerial system (cUAS) capabilities that reduce risk to the warfighter while allowing the community to keep pace with the threat. DDS solutions are vital to ensuring protection from adversary UAS operations that threaten DoD assets in the U.S., and around the world."
- cUAS Branch Head, Naval Air Warfare Center, Aircraft Division (NAWCAD)
Program Spotlight
Hack the Pentagon

Hack the Pentagon (“HtP”) leverages the power of the crowd on priority critical cybersecurity initiatives to substantially improve the DoD's cyber defenses through a series of “bug bounties”. In a bug bounty, DDS works with asset owners, industry partners and independent security researchers to discover and document vulnerabilities. With this approach, DDS helps the Department quickly mitigate vulnerabilities to strengthen the DoD's cybersecurity posture.

Recent News

PODCAST: DDS Director, Jennifer Hay, on how to build better in government
Technology should empower, not hinder, the mission, and with an emphasis on a user-centric approach, Hay highlights DDS's focus on discovery and deep user understanding to create impactful solutions.
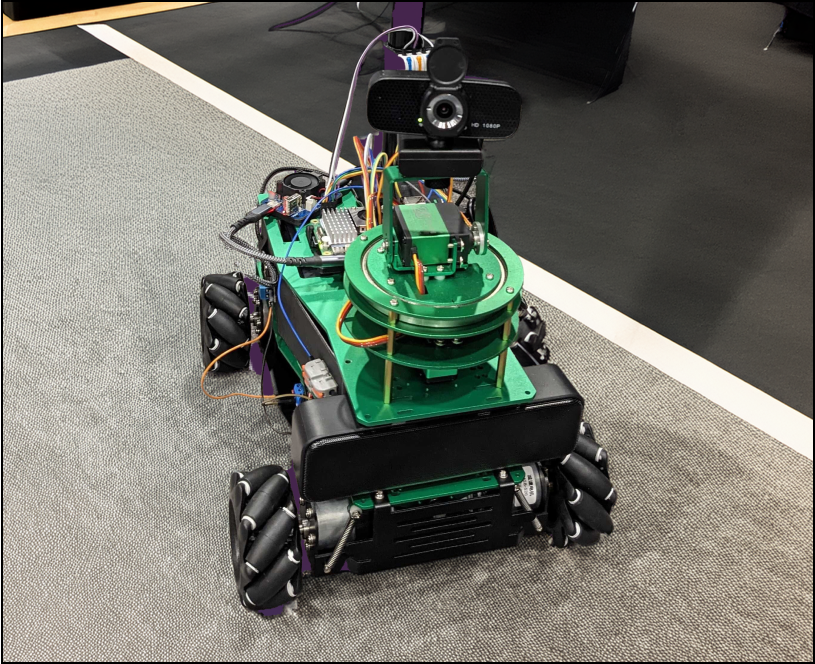
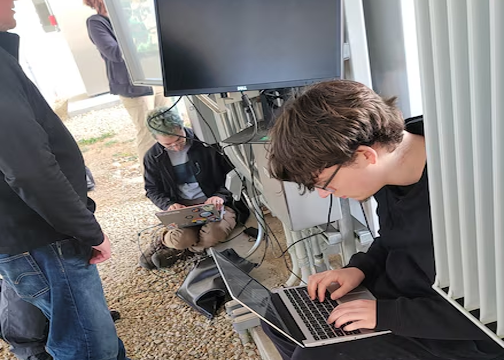
AI-powered 'Combee' robot shows how voice commands can transform defense operations
Robots are getting a boost thanks to artificial intelligence. Even the Department of Defense is getting involved.
 This image was cropped to emphasize the subject.
This image was cropped to emphasize the subject.U.S. Army Reserve Establishing Energy Microgrid Cyber Resilience Protocols
The Army Reserve Installation Management Directorate and Fort Hunter Liggett, in cooperation with the Defense Digital Service (DDS) and industry-partner Bugcrowd, conducted the “Hack the Army Microgri...